Analysis of a Multi-Stage Cyber Attack on Helios Financial Services
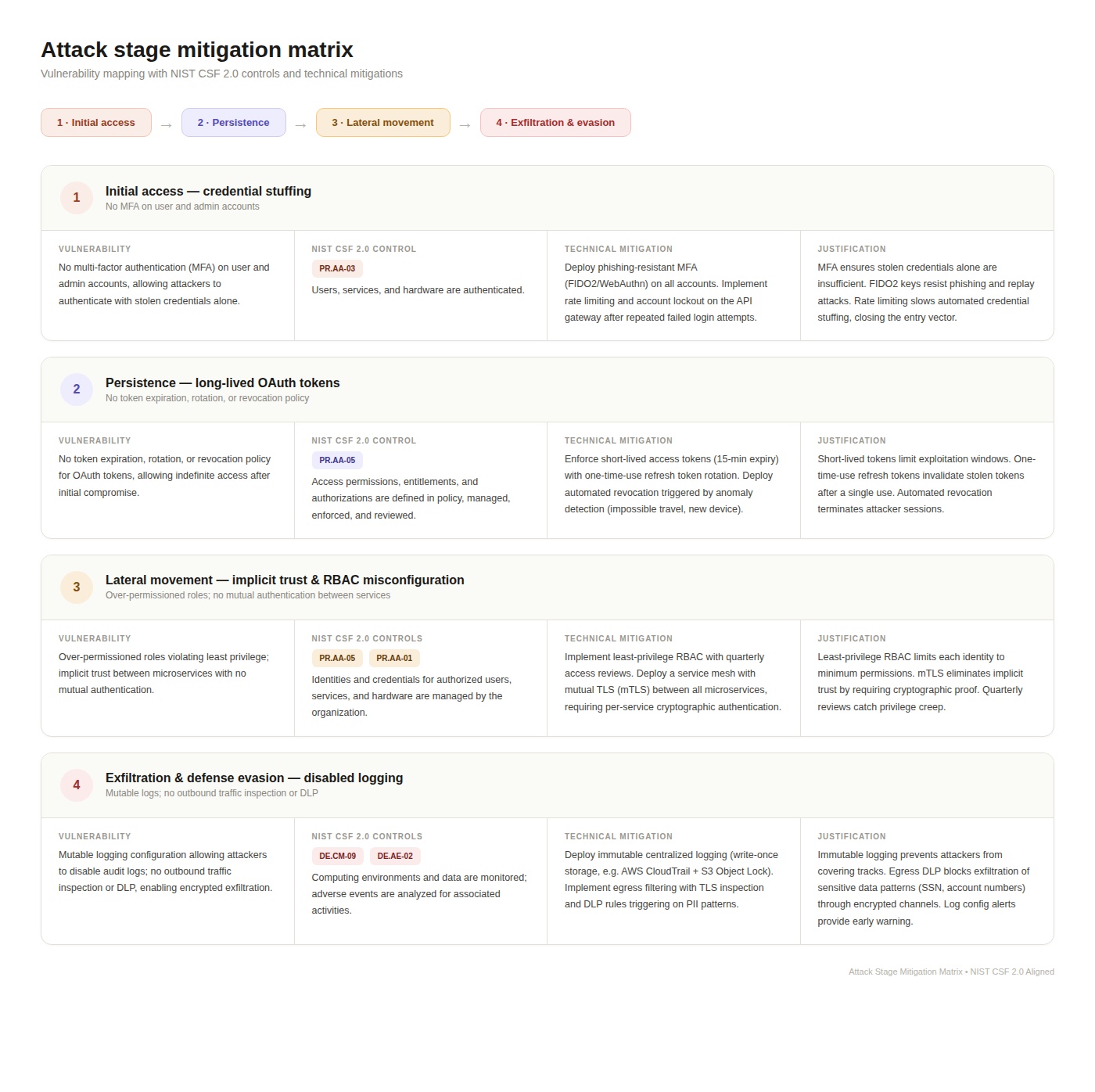
Activity 1: Attack Stage Identification and Corresponding Vulnerabilities Helios is a cloud-based financial services provider delivering web and mobile banking solutions. Their architecture includes a customer-facing API gateway, an IAM system using SSO/OAuth, and a centralized data platform storing PII and financial records. The company suffered a multi-stage attack that progressed through four distinct phases. The following analysis identifies each attack stage and the underlying vulnerability that enabled it. Stage 1: Initial Access — Credential Stuffing The attackers used credential stuffing to gain initial access. Credential stuffing is an automated attack that uses breached username/password pairs from other compromised services to attempt authentication against a target system. Because users frequently reuse passwords across platforms, a percentage of these credentials will be valid. The vulnerability that enabled this stage was the absence of Multi-Factor Authentication (MFA) on Helios’s authentication system. Without MFA, a correct password alone was sufficient to authenticate, giving the attackers a foothold in the environment. Stage 2: Persistence — Long-Lived OAuth Tokens After gaining initial access, the attackers established persistence by obtaining long-lived OAuth tokens. OAuth tokens (access tokens and refresh tokens) are issued after successful authentication and are used to authorize subsequent API requests without re-entering credentials. If access tokens have excessively long lifetimes, or if refresh tokens can be reused indefinitely without rotation or revocation, an attacker can maintain persistent access without needing the original credentials again. The vulnerability was the lack of a proper token lifecycle management policy, specifically the absence of short token expiry times, one-time-use refresh token rotation, and anomaly-triggered token revocation. Stage 3: Lateral Movement — Implicit Trust and RBAC Misconfiguration The attackers moved laterally across Helios’s internal systems by exploiting two related vulnerabilities. First, implicit trust relationships between microservices meant that internal services did not require mutual authentication; if one service was compromised, it could freely communicate with others. Second, Role-Based Access Control (RBAC) was misconfigured with over-permissioned roles, violating the principle of least privilege. The compromised identity inherited excessive permissions, enabling the attackers to pivot from the initially compromised service to systems storing sensitive data. Stage 4: Exfiltration and Defense Evasion — Disabled Logging and Encrypted Exfiltration In the final stage, the attackers disabled logging on key API endpoints, blinding the SIEM (Security Information and Event Management) system. With logging disabled, the attacker’s activities generated no alerts. They then exfiltrated PII and financial records through encrypted outbound traffic. Two vulnerabilities enabled this: first, the logging configuration was mutable, meaning an attacker with sufficient privileges could disable it; and second, the absence of outbound traffic inspection and Data Loss Prevention (DLP) controls meant encrypted exfiltration channels went undetected. Activity 2: NIST CSF 2.0 Control Mapping The following table maps each attack stage to a specific NIST CSF 2.0 subcategory, identifies a technical mitigation control, and provides a justification for how that control improves Helios’s security posture.
Activity 3: NIST CSF and SOC 2 Trust Services Criteria Complementary Analysis Selected Control: PR.AA-03 — Multi-Factor Authentication NIST CSF 2.0 subcategory PR.AA-03 states that users, services, and hardware are authenticated. Implementing phishing-resistant MFA (FIDO2/WebAuthn) under this control directly addresses the credential stuffing vulnerability that enabled the initial access stage of the Helios breach. This NIST CSF control complements multiple SOC 2 Trust Services Criteria to ensure Helios remains both technically secure and demonstrably compliant while handling sensitive government financial data. Mapping to SOC 2 CC Criteria CC6.1 (Logical Access Security): CC6.1 requires the entity to implement logical access security software, infrastructure, and architectures to protect information assets from security events. The CC6.1 points of focus explicitly reference multifactor authentication as a mechanism for identifying and authenticating users. Deploying FIDO2 MFA under PR.AA-03 directly satisfies this criterion by ensuring that authentication to the API gateway and IAM system requires a cryptographic second factor, preventing unauthorized access even when passwords are compromised. CC6.2 (Credential Registration and Removal): CC6.2 requires the entity to register and authorize users before issuing system credentials, and to remove credentials when access is no longer authorized. The MFA enrollment process enforces identity verification before a second factor (hardware key, authenticator app) is registered. This ensures only verified users receive access credentials. Additionally, MFA device deregistration processes align with CC6.2’s requirement to remove credentials when access is revoked. CC6.3 (Role-Based Authorization with Least Privilege): CC6.3 requires access to be authorized based on roles, least privilege, and segregation of duties. MFA complements RBAC by ensuring that even if authorization policies are correctly configured, the authenticated identity must still prove itself through a second factor. This creates a defense-in-depth approach where both authentication and authorization must be satisfied before access is granted. CC7.2 (Anomaly Monitoring): CC7.2 requires the entity to monitor system components for anomalies indicative of malicious acts. MFA systems generate authentication event logs, including failed MFA challenges, new device enrollments, and impossible-travel detections. These events feed directly into the SIEM, providing the anomaly detection data SOC 2 CC7.2 requires. In the Helios scenario, MFA would have generated alerts during the credential stuffing phase, enabling earlier detection. CC5.2 (Technology General Controls): CC5.2 requires the entity to select and develop general control activities over technology to support the achievement of objectives. Implementing MFA is a documented, auditable risk mitigation control. During a SOC 2 Type II audit, the auditor can verify that MFA is configured, enforced, and monitored, providing direct evidence that Helios is actively mitigating credential-based attack risks. Complementary Relationship NIST CSF 2.0 defines the technical control (what to implement and where it fits in the security architecture). SOC 2 Trust Services Criteria define the compliance requirements (how an auditor evaluates whether the control is in place, operating effectively, and documented). Together, they ensure that Helios is both technically protected against credential-based attacks and able to demonstrate compliance to auditors, regulators, and government clients. For a FinTech company handling sensitive government financial data, this dual assurance, covering both technical effectiveness and auditable compliance, is a mandatory requirement for maintaining operational trust and regulatory standing. References National Institute of Standards and Technology. (2024, February 26). The NIST Cybersecurity Framework (CSF) 2.0 (NIST CSWP 29). https://nvlpubs.nist.gov/nistpubs/CSWP/NIST.CSWP.29.pdf American Institute of Certified Public Accountants. (2022). 2017 Trust Services Criteria for Security, Availability, Processing Integrity, Confidentiality, and Privacy (With Revised Points of Focus — 2022). AICPA.